Ransomware Shut Down Mississippi's Biggest Hospital for 9 Days. Here's What Clinics Need to Do Now.
On February 19, 2026, doctors and nurses at the University of Mississippi Medical Center arrived for their shifts and found their systems locked.
EPIC — gone. Billing — gone. Appointment scheduling — gone. The entire network, dark.
For nine days, 10,000 staff at Mississippi’s only Level I trauma center, only children’s hospital, and only organ transplant program operated on pen and paper. Cancer patients had infusion appointments rescheduled. Surgeries were cancelled. The Medusa ransomware group later claimed responsibility.
UMMC is one of the largest, best-resourced healthcare organizations in the Southeast. If it can happen to them, it can happen to any clinic, practice, or hospital system that hasn’t prepared.
Why Healthcare Is Ransomware’s Favorite Target
Medusa is a ransomware-as-a-service operation with over 366 claimed attacks, heavily concentrated on healthcare. They don’t just encrypt files — they steal patient data first, then threaten to publish it if the ransom isn’t paid. Double extortion is now standard in 96% of healthcare ransomware cases.
Healthcare is the target for structural reasons. Patient care depends on immediate access to records, medication histories, and lab results. That pressure to restore systems quickly translates directly into willingness to pay — and attackers know it.
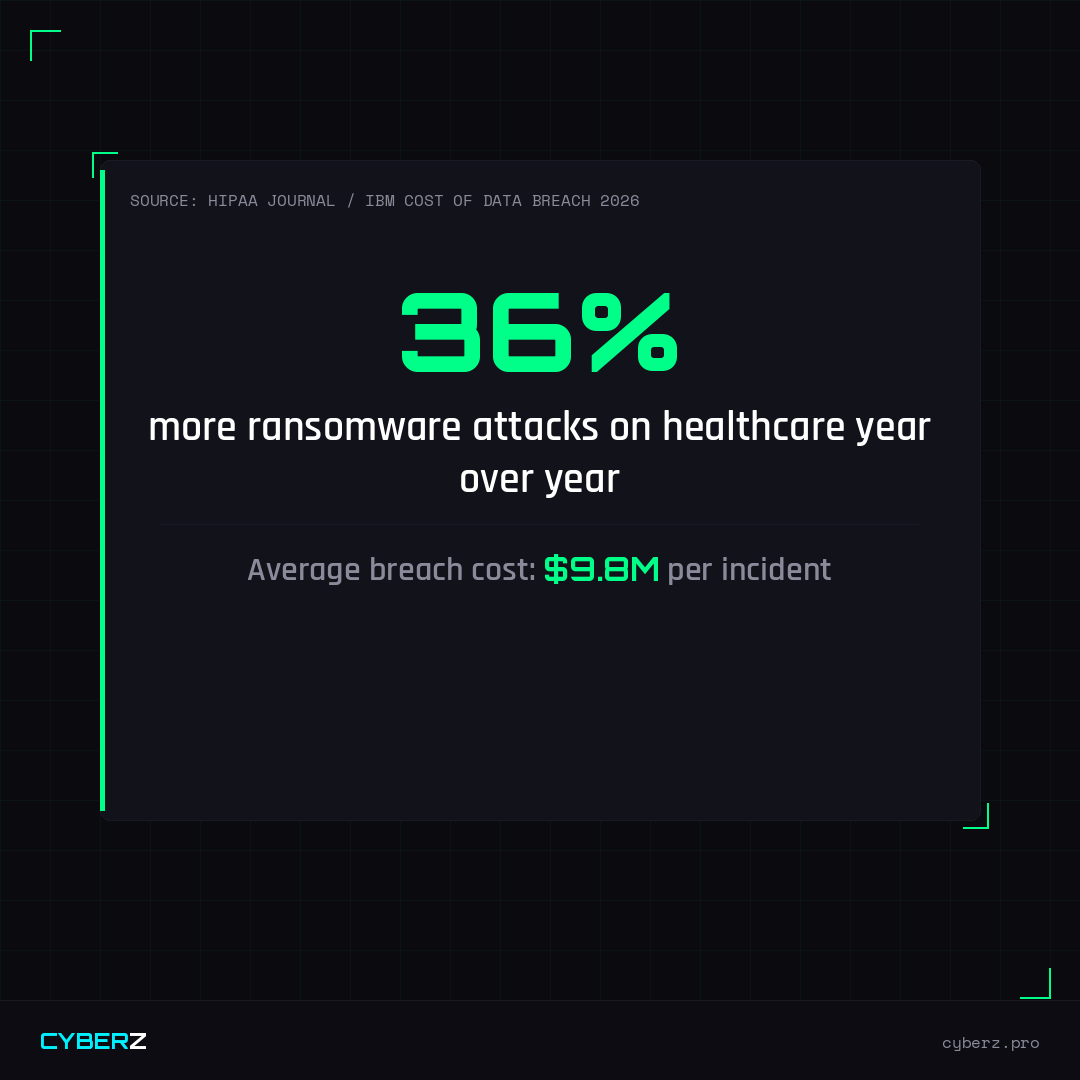
Ransomware attacks on healthcare surged 36% in late 2025. The sector accounts for over one-third of all ransomware incidents, with breach costs averaging between $7.4M and $9.8M per incident.
How Attacks Get In
The entry points haven’t changed much — but the speed and scale have:
Phishing emails remain the #1 vector. One click from one staff member on a fake vendor email or spoofed patient portal notification can hand attackers a foothold.
Legacy systems and medical devices running Windows 7 or older operating systems can’t be patched without FDA re-certification. Attackers specifically scan for these using AI-assisted tools.
Third-party vendors are increasingly the entry point. Ransomware groups have shifted to targeting healthcare vendors — billing companies, IT providers, software platforms — because breaching one vendor can compromise dozens of healthcare organizations simultaneously.
What UMMC’s 9 Days Looked Like
Without access to EPIC, staff had to:
- Record patient information by hand
- Manage medications and dosages from memory or printed records
- Reschedule all non-emergency procedures
- Coordinate transfers through backup phone systems
This is not a hypothetical. This is what operational failure looks like in a healthcare setting. The human cost extends beyond the financial.
What Every Clinic Needs Before It Happens to Them
// HEALTHCARE RANSOMWARE READINESS CHECKLIST
- Tested, isolated backups — not just cloud sync, but air-gapped or immutable copies you can actually restore from
- Network segmentation — medical devices and clinical systems on separate networks from administrative systems
- MFA on all staff accounts, especially email and EHR access
- Documented incident response plan with clear roles, communication templates, and backup workflows
- Phishing simulation training quarterly — not annually
- Vendor/BAA risk assessments for all third-party software and service providers
- Written HIPAA Security Risk Assessment updated within the past 12 months
- Cyber insurance with ransomware coverage reviewed and confirmed
If You’re Attacked
Speed matters. The first 72 hours determine whether you recover or pay.
- Isolate affected systems immediately — disconnect from the network, don’t shut down unless instructed by your IR team
- Call your incident response provider or cyber insurer — most policies include IR support
- Notify HHS/OCR within 60 days if PHI was involved (72 hours for covered entities under the 2026 HIPAA updates)
- Do not delete anything — logs, emails, and system images are evidence
- Do not pay without consulting legal and law enforcement — the FBI recommends against payment
Healthcare Security Bundle
20+ documents covering ransomware response, HIPAA compliance, breach notification, staff training, and vendor risk — built specifically for clinics, practices, and healthcare organizations.
View Bundle →Originally reported by The Record / HIPAA Journal for The Record / HIPAA Journal on February–March 2026.